wooooohooooo i managed to get it running 
i used the alternate installer (which is available for 20.04). it is not as comfortable as with the live, because you cant use ssh to copy the loooooooong encryption keys, it works.
so what i've done....
- boot server live installer and set keyboard language
- change to console window with alt-f2
- edit /etc/ssh/sshd_config to allow root login
- systemctl restart sshd
- set root pw
- ssh in and create partions e.g.
Code:
export DEV=/dev/sda
sgdisk --new=1:0:+1G $DEV
sgdisk --new=2:0:+2M $DEV
sgdisk --new=3:0:+128M $DEV
sgdisk --new=5:0:0 $DEV
sgdisk --typecode=1:8301 --typecode=2:ef02 --typecode=3:ef00 --typecode=5:8301 $DEV
sgdisk --change-name=1:/boot --change-name=2:GRUB --change-name=3:EFI-SP --change-name=5:rootfs $DEV
sgdisk --hybrid 1:2:3 $DEV
sgdisk --print $DEV
Code:
cryptsetup luksFormat --type=luks1 /dev/sda1
cryptsetup luksFormat /dev/sda5
cryptsetup open /dev/sda1 LUKS_BOOT
cryptsetup open /dev/sda5 sda5_crypt
Code:
mkfs.ext4 -L boot /dev/mapper/LUKS_BOOT
mkfs.vfat -F 16 -n EFI-SP /dev/sda3
- create lvm on top of luks (for / and swap)
Code:
pvcreate /dev/mapper/sda5_crypt
vgcreate ubuntu-vg /dev/mapper/sda5_crypt
lvcreate -L 4G -n swap_1 ubuntu-vg
lvcreate -l 80%FREE -n root ubuntu-vg
- reboot and boot from alternate installer, continue till keyboard language is set
- alt-f2 to change to console
- mount luks partitions
Code:
cryptsetup open /dev/sda1 LUKS_BOOT
cryptsetup open /dev/sda5 sda5_crypt
- alt-f1 to move back to the installer
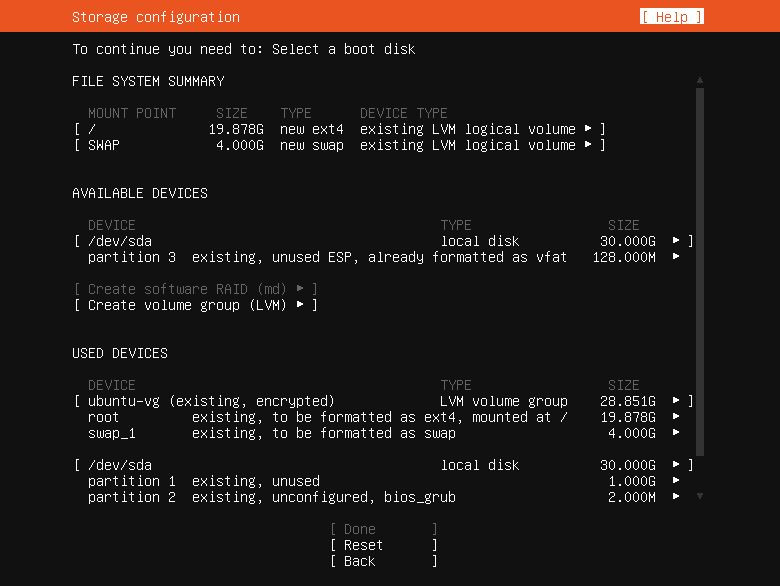
- continue till disk setup -> manual
- swap -> use as swap
- sda5_crypt-ubuntu-vg-root -> ext4 + format -> mountpoint /
- LUKS_BOOT -> ext4 + format -> mountpoint /boot
- save layout and continue
- continue installer till bootloader -> do not proceed yet
- alt-f2 to console
- create folders under /target/etc if they do not exist and execute
Code:
echo "GRUB_ENABLE_CRYPTODISK=y" > /target/etc/default/grub.d/local.cfg
- alt-f1 to installer and install bootloader
- alt-f2 to console and run the following commands
Code:
mount /dev/mapper/ubuntu--vg-root /target
for n in proc sys dev etc/resolv.conf; do mount --rbind /$n /target/$n; done
chroot /target
mount -a
apt install -y cryptsetup-initramfs
echo "KEYFILE_PATTERN=/etc/luks/*.keyfile" >> /etc/cryptsetup-initramfs/conf-hook
echo "UMASK=0077" >> /etc/initramfs-tools/initramfs.conf
mkdir /etc/luks
dd if=/dev/urandom of=/etc/luks/boot_os.keyfile bs=512 count=1
chmod u=rx,go-rwx /etc/luks
chmod u=r,go-rwx /etc/luks/boot_os.keyfile
cryptsetup luksAddKey /dev/sda1 /etc/luks/boot_os.keyfile
cryptsetup luksAddKey /dev/sda5 /etc/luks/boot_os.keyfile
echo "LUKS_BOOT UUID=$(blkid -s UUID -o value /dev/sda1) /etc/luks/boot_os.keyfile luks,discard" >> /etc/crypttab
echo "sda5_crypt UUID=$(blkid -s UUID -o value /dev/sda5) /etc/luks/boot_os.keyfile luks,discard" >> /etc/crypttab
update-initramfs -u -k all
- reboot and enjoy a fully encrypted system

credits go to this tut Full_Disk_Encryption_Howto_2019 - Community Help Wiki (ubuntu.com) - i only changed it to match the server version which was not too straightforward. so hopefully the ubuntu guys fix this flaw in the live installer soon
enjoy!




 Adv Reply
Adv Reply




Bookmarks