Reboot into your New System
Skipping other parts of the installation, that should leave you all setup to reboot and boot into your new encrypted system.
Enjoy your nice new password prompt at Usplash.

Part Two
HowTO: Setup Keyfile for Disk Encryption at Boot
Introduction
This is the second part of the two part guide.
The inspiration for this guide mostly comes from an article I read in the Guardian, a British daily newspaper.
The internet version of that article can be read here: http://www.guardian.co.uk/technology...ction-internet
This provoked thoughts and ideas about how I will implement my contingency plan.
What I came up with was to use an existing feature of dm-crypt - a Keyfile - and that keyfile now lives on an SD card to which my family is in possession of.
This guide documents my steps to implementing this.
Create Keyfile
There are numerous ways to produce a keyfile, you can look them up and compare, but I prefer this method:
Code:
head -c 4096 /dev/urandom > .netbook.key
Then to add the keyfile to the Luks partition keyring, run:
Code:
sudo cryptsetup luksAddKey /dev/sda1 .netbook.key
Once that is all done, move the keyfile to a USB drive or SD Card.
For example:
Code:
mv .netbook.key /media/disk/.netbook.key
Create a Safeboot
Before making any dia changes that may leave your system in an unbootable state. Make a backup of your initrd.img
To find out what the initrd you use:
Code:
ls /boot/initrd.img*
If you run Ubuntu Jaunty, at this time of writing, you will get initrd.img-2.6.28-15-generic as the output from that.
Now, whatever the name, make a copy of it:
Code:
sudo cp -a /boot/initrd.img-2.6.28-15-generic /boot/initrd.img-2.6.28-15-generic-safe
And add a new boot stanza menu.lst file if you use Grub as your bootloader.
Code:
gksudo gedit /boot/grub/menu.lst
and copy your main boot stanza to the bottom, and make the following changes you can see below.
Once complete, save and quit.
Code:
## ## End Default Options ##
title Ubuntu 9.04, kernel 2.6.28-15-generic
uuid b7c89e2d-ac2d-4d74-81cf-64c7483d4aa0
kernel /vmlinuz-2.6.28-15-generic root=/dev/mapper/netbook-root ro quiet splash quiet
initrd /initrd.img-2.6.28-15-generic
quiet
title Ubuntu 9.04, kernel 2.6.28-15-generic (recovery mode)
uuid b7c89e2d-ac2d-4d74-81cf-64c7483d4aa0
kernel /vmlinuz-2.6.28-15-generic root=/dev/mapper/netbook-root ro single
initrd /initrd.img-2.6.28-15-generic
title Ubuntu 9.04, memtest86+
uuid b7c89e2d-ac2d-4d74-81cf-64c7483d4aa0
kernel /memtest86+.bin
quiet
### END DEBIAN AUTOMAGIC KERNELS LIST
title Ubuntu 9.04, kernel 2.6.28-15-generic (safe boot)
uuid b7c89e2d-ac2d-4d74-81cf-64c7483d4aa0
kernel /vmlinuz-2.6.28-15-generic root=/dev/mapper/netbook-root ro quiet splash quiet
initrd /initrd.img-2.6.28-15-generic-safe
quiet
If you use Grub2 as your bootloader, as is the default with Ubuntu Karmic and later releases, then you will have a slightly different way to implement this. But until it is released, this won't be included in this guide.
Add Modules to Ramdisk
OK, with the backup setup, it's now time to edit the bootloader files.
First, we have the ramdisk to change.
Code:
gksudo gedit /etc/initramfs-tools/modules
And add the following to the bottom of the file
Code:
## Crypt Key Lines
# USB Devices
usb_storage
# SD Cards
ricoh_mmc
sdhci_pci
sdhci
# Fat Filesystems
fat
vfat
nls_cp437
nls_iso8859-1
nls_utf8
# Ext2 Filesystem modules are built into kernel
# Uncomment if `grep ext2 /proc/modules` has output
#ext2
Save and quit.
Decrypt Script
Next, is to create the decrypt script.
Firstly, it is not perfect, and may require tweaking to get it right, but it should work on all machines generically so long as you keep to the following guideline:
- The keyfile is on a /dev/sd* or a /dev/mmcbk* drive.
- The keyfile is on a ext2 or vfat filesystem.
or The keyfile is on a filesystem to whom's modules are built into the kernel. - The keyfile is on the First Primary Partition on the disk (ie: sda1, sdb1, mmcbk1p1)
I must also note the following too:
- If present, this script will work with Usplash in the first instance.
- If present, this script will work with stty in the second instance.
- Else this script will give you a warning that the password may be visible on screen.
Ubuntu uses Usplash by default, but different people prefer to have different setups, and so they may have the script work differently for them.
OK, with that said and understood, open a file:
And paste the following in:
Code:
#!/bin/sh
# Key file in the USB disk
KEYFILE=.netbook.key
USPLASH=0
if [ -p /dev/.initramfs/usplash_outfifo -a -x /sbin/usplash_write ]; then
/sbin/usplash_write "VERBOSE on"
if [ $? -eq 0 ]; then
USPLASH=1
/sbin/usplash_write "CLEAR"
fi
fi
STTY=0
STTYCMD=false
if [ -x /bin/stty ]; then
STTY=1
STTYCMD=/bin/stty
elif [ `(busybox stty >/dev/null 2>&1; echo $?)` -eq 0 ]; then
STTY=1
STTYCMD="busybox stty"
fi
msg ()
{
if [ $# -gt 0 ]; then
echo $2 | while read LINE; do
if [ $USPLASH -eq 1 ]; then
/sbin/usplash_write "$1 $LINE"
else
echo $3 "$2" >&2
fi
done
fi
}
readpass ()
{
if [ $# -gt 0 ]; then
if [ $USPLASH -eq 1 ]; then
usplash_write "INPUTQUIET $1: "
PASS="$(cat /dev/.initramfs/usplash_outfifo)"
else
[ $STTY -ne 1 ] && msg TEXT "WARNING stty not found, password will be visible"
echo -n "$1" >&2
$STTYCMD -echo
read -r PASS </dev/console >/dev/null
[ $STTY -eq 1 ] && echo >&2
$STTYCMD echo
fi
fi
if [ -z "$PASS" ]; then
exec "$0" "$2"
fi
echo -n "$PASS"
}
MD=/tmp-usb-mount
if [ "x$1" = "x" -o "x$1" = "xnone" ]; then
KEYF=$KEYFILE
else
KEYF=$1
fi
USBLOAD=0
MMCLOAD=0
cat /proc/modules | busybox grep usb_storage >/dev/null 2>&1
USBLOAD=$?
cat /proc/modules | busybox grep mmc >/dev/null 2>&1
MMCLOAD=$?
if [ $USBLOAD -gt 0 -o $MMCLOAD -gt 0 ]; then
modprobe usb_storage >/dev/null 2>&1
modprobe ricoh_mmc >/dev/null 2>&1
modprobe mmc_block >/dev/null 2>&1
modprobe sdhci_pci >/dev/null 2>&1
modprobe sdhci >/dev/null 2>&1
fi
sleep 7
OPENED=0
ls -d /sys/block/sd* >/dev/null 2>&1
SDS=$?
if [ $SDS -eq 0 ]; then
echo "Trying to get the key from USB keychain ..." >&2
mkdir -p $MD
for SFS in /sys/block/sd*; do
DEV=`busybox basename $SFS`
F=$SFS/${DEV}1/dev
if [ 0`cat $SFS/removable` -eq 1 -a -f $F ]; then
echo "> Trying device: $DEV ..." >&2
FSTYPE=`cat /dev/.udev/db/*${DEV}1 | busybox sed -n 's/.*ID_FS_TYPE=\(.*\)/\1/p'`
echo "> Filesystem type $FSTYPE ..." >&2
cat /proc/modules | busybox grep $FSTYPE >/dev/null 2>&1
FSLOAD=0$?
if [ $FSLOAD -gt 0 ]; then
modprobe $FSTYPE >/dev/null 2>&1
fi
mount /dev/${DEV}1 $MD -t $FSTYPE -o ro 2>/dev/null
if [ -f $MD/$KEYF ]; then
cat $MD/$KEYF
umount $MD 2>/dev/null
OPENED=1
break
fi
umount $MD 2>/dev/null
fi
done
fi
ls -d /sys/block/mmcblk* >/dev/null 2>&1
MMCS=$?
if [ $MMCS -eq 0 -a $OPENED -eq 0 ]; then
echo "Trying to get the key from MMC keychain ..." >&2
mkdir -p $MD
for SFS in /sys/block/mmcblk*; do
DEV=`busybox basename $SFS`
F=$SFS/${DEV}p1/dev
if [ 0`cat $SFS/removable` -eq 1 -a -f $F ]; then
echo "> Trying device: $DEV ..." >&2
FSTYPE=`cat /dev/.udev/db/*${DEV}p1 | busybox sed -n 's/.*ID_FS_TYPE=\(.*\)/\1/p'`
echo "> Filesystem type $FSTYPE ..." >&2
cat /proc/modules | busybox grep $FSTYPE >/dev/null 2>&1
FSLOAD=0$?
if [ $FSLOAD -gt 0 ]; then
modprobe $FSTYPE >/dev/null 2>&1
fi
mount /dev/${DEV}p1 $MD -t $FSTYPE -o ro 2>/dev/null
if [ -f $MD/$KEYF ]; then
cat $MD/$KEYF
umount $MD 2>/dev/null
OPENED=1
break
fi
umount $MD 2>/dev/null
fi
done
fi
[ $USPLASH -eq 1 ] && msg STATUS " " && msg CLEAR ""
if [ $OPENED -ne 1 ]; then
# If you wish to change the error message, change it here:
msg TEXT "FAILED to find suitable USB key-file ..."
msg TEXT "If this is your first attempt, try removing and reinserting the key device,"
msg TEXT "wait five seconds for all devices to settle, then press Enter."
msg TEXT "Else, enter the LUKS password to decrypt the disk."
readpass "Password" "$1"
else
msg TEXT "Success loading key-file from $SFS"
fi
[ $USPLASH -eq 1 ] && /sbin/usplash_write "VERBOSE default"
Save the file and install it into your system:
Code:
sudo install keyscript.sh /usr/local/sbin/keyscript.sh
Alter Crypttab
Lastly, we need to change the crypttab file to include the keyscript in the decrypt process.
Code:
gksudo gedit /etc/crypttab
You should not copy and paste any of the code text outlined here.
If you look carefully at your own crypttab file, you should see something like this:
Code:
sda1_crypt /dev/disk/by-uuid/b7c89e2d-ac2d-4d74-81cf-64c7483d4aa0 none luks
First, what you do, is make a copy of that line:
Code:
sda1_crypt /dev/disk/by-uuid/b7c89e2d-ac2d-4d74-81cf-64c7483d4aa0 none luks
sda1_crypt /dev/disk/by-uuid/b7c89e2d-ac2d-4d74-81cf-64c7483d4aa0 none luks
Then comment out the first line and alter the second.
To comment on the bits in red.
.netbook.key is the name of the keyfile, as found on the external storage device.
ie: if your external device is /dev/sdb1, mounted on /media/disk, and the keyfile is located /media/disk/.keyfile/mykey
Then you would have the following:
Code:
sda1_crypt /dev/disk/by-uuid/b7c89e2d-ac2d-4d74-81cf-64c7483d4aa0 .keyfile/mykey luks,keyscript=/usr/local/sbin/keyscript.sh
keyscript=/usr/local/sbin/keyscript.sh is the location of the script file, you should have installed it in the location above - if you installed it elsewhere, specify.
The ending result should look like the following changes as you can see outlined here:
Code:
#sda1_crypt /dev/disk/by-uuid/b7c89e2d-ac2d-4d74-81cf-64c7483d4aa0 none luks
sda1_crypt /dev/disk/by-uuid/b7c89e2d-ac2d-4d74-81cf-64c7483d4aa0 .netbook.key luks,keyscript=/usr/local/sbin/keyscript.sh
If you are happy that everything looks fine, save and quit.
Update Ramdisk and Reboot
And that is hopefully it!
Just update the ramdisk:
Code:
sudo update-initramfs -u all
and then reboot your system.
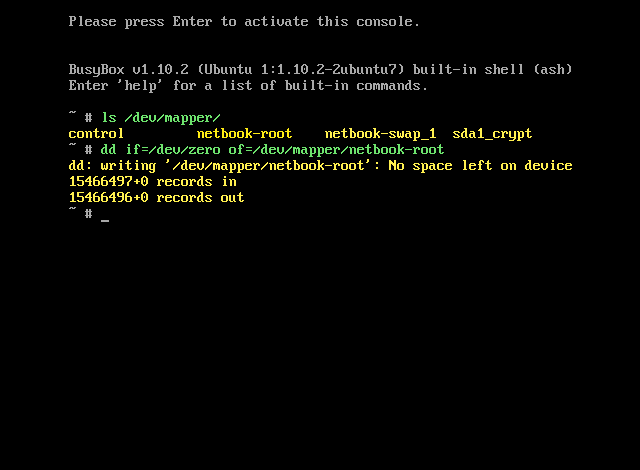
If the script fails to detect the device that your keyfile is on/you don't plug in the device at boot, this is the message that you get.

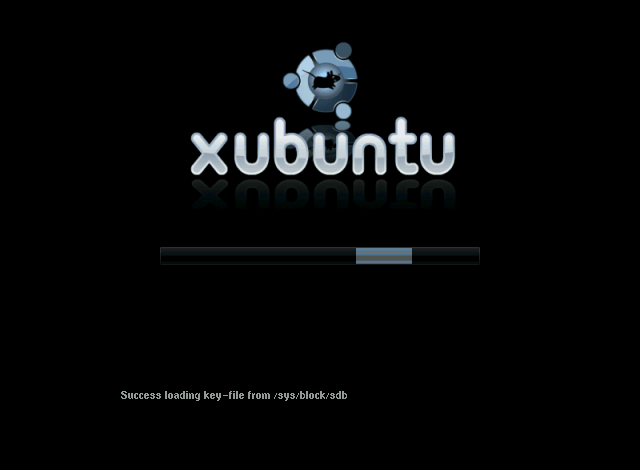
If all is a success, then you will receive this message, and Ubuntu will continue to boot as normal.
Testimonials and Improvements
If you have any testimonies, queries or improvement suggestion. Please shout and I will be happy to help.
Regards
Iain









 Adv Reply
Adv Reply





Bookmarks